
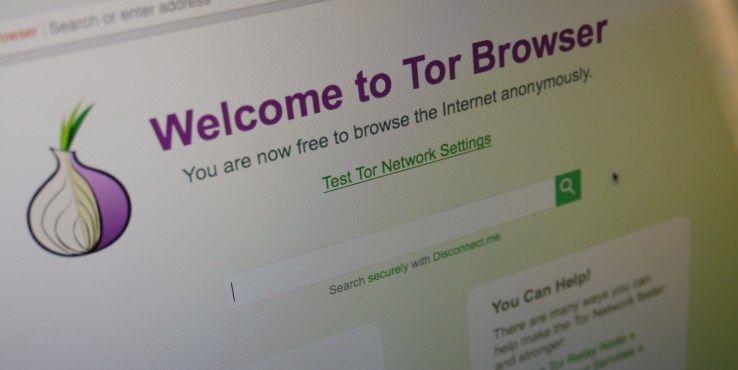
The leaking of classified documents detailing the data collection activities of the U.S. National Security Agency earlier this year reignited some long-standing concerns about the vulnerability of enterprise data stored in the cloud.
Experts have predicted, that leaks about the NSA spy programs are driving some long overdue changes in enterprise and service provider security and privacy policies.
When Edward Snowden first began spilling details of the NSA’s surveillance practices via metadata to selected reporters in June, industry analysts had expected that it would dampen plans for cloud deployment.
For instance, the Information Technology & Innovation Foundation in August said the leaks could cause U.S. cloud providers to lose up to $35 billion in potential sales through 2016.
Another industry group, the Cloud Security Alliance, predicted a similar backlash due to concerns by European companies that the U.S. government would access to their data.
Six months later, now the impact appears to be less severe than anticipated.
Despite some reports of slowing sales of cloud services by U.S. vendors to overseas companies, experts now expect that the Snowden leaks will have little effect on long-term sales. The business benefits of using cloud-based services continue to supersede enterprise fears of government snooping.
At the same time though, the detailing of classified NSA spy programs has prompted an increased emphasis on cloud data security and protection that’s expected to grow further in 2014.
Analysts say IT security officials are looking at several key areas, such as data encryption, key management and data ownership, regionalization, and the need for increased government transparency, to improve cloud security.
Data encryption
Encryption has gained a lot of attention since the Snowden leaks. Major service providers like Microsoft, Yahoo and Google set the tone by adding end-to-end encryption of data they host and manage for customers.
For instance, Google Cloud Storage now automatically encrypts all new data before it’s written to disk. Such server-side encryption will soon be available for older data stored in Google clouds.
Since the NSA programs were disclosed, Microsoft has announced that it plans to ramp up encryption support for various services, including Outlook.com, Office 365, SkyDrive and Windows Azure.
By the end of 2014, Microsoft expects to have measures in place for encrypting data in transit between customer locations and its data centers, and while in transit between its own data centers.
Like Google, Microsoft says it plans to encrypt all stored data in the cloud
Several other cloud services providers, like Dropbox, Sonic.net and SpiderOak, have announced support for similar data encryption programs, and for features like 2048-bit key lengths and the “Perfect Forward Secrecy” method for future-proofing encrypted data.
Information in the classified documents about NSA attempts to weaken encryption algorithms, and to tap fiber links connecting service provider data centers provided much of the force for these efforts.
Meanwhile, large U.S.-based cloud service providers are setting up service operations in different parts of the world in part to lower delivery costs and deliver better performance to local customers.
Back in December, for instance, Amazon announced that it plans to start delivering Amazon Web Services products in China starting 2014. The plan calls for the company to install cloud servers in China facilities to deliver hosted services to businesses in that country.
Concerns stemming from the Snowden affair definitely will force the government to be more transparent about data collection programs.
Google, Microsoft, Yahoo and an array of other high-technology vendors are now pressing the government to allow them to disclose details about secret requests for customer data by the NSA and other intelligence agencies. The companies argue that laws prohibiting them disclosing details of such requests have created false perceptions about their role in government data collection activities.
Google, Microsoft and others plan to provide more details in their periodic Transparency Reports, and have indicated a willingness to legally challenge certain government requests for data.
Verizon, for instance, says it plans to soon release a Transparency Report that details law enforcement requests for its customer data.

































































You must be logged in to post a comment.